Governance, Risk, Compliance (GRC) Software
All-in-one GRC platform for structured process control, risk mitigation, and automated compliance.
🟢 Risk, compliance, audit & third-party oversight
🟢 Integrating regulatory best practices
🟢 Automated workflows and real-time dashboard
🟢 AI-driven efficiency










































Connect risk and compliance data
in one GRC tool

Increase visibility on risks
Get a real-time overview of all risks in one place. Track ownership, impact, and trends effortlessly.

Ensure compliance with ease
Stay ahead of evolving regulations like DORA, ISO and more. Automate controls to ensure consistent, audit-proof compliance.

Eliminate manual reporting & audits
Replace spreadsheets with smart, connected reporting. Save time and reduce errors with Power BI integration.
Identify, assess, and monitor risks
Gain a centralized view of all your strategic and operational risks with real-time dashboards, automated scoring, and clear ownership.
CERRIX connects all three lines of defense (3LoD), enabling integrated risk ownership, control effectiveness monitoring, and data-driven prioritization via configurable dashboards and risk registers.
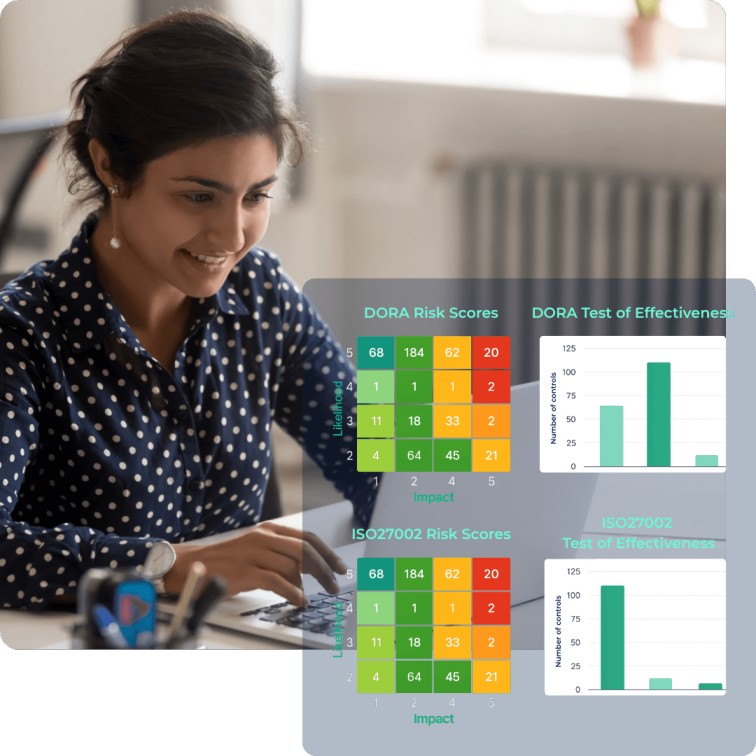
Stay fully compliant with evolving regulations
Turn regulatory complexity into structured, audit-ready controls. CERRIX supports frameworks like DORA, ISO 27001, NIS2, and Solvency II.
Automate your control framework with pre-mapped templates, frequency-based control testing, and real-time status updates. Centralize policy management and audit evidence collection to ensure full traceability and reduce compliance fatigue.
Connect risks data for real-time insights
Move beyond spreadsheets with structured, real-time dashboards powered by integrated control data and audit trails.
From automated control testing to board-ready reporting via Power BI, CERRIX ensures transparency, accountability, and faster responses—supporting internal audit, external regulators, and executive oversight with evidence-backed clarity.
.jpg)
A modular platform for integrated governance, risk, compliance.
CERRIX brings structure to the way your teams manage risk and compliance oversights,
collaborate across functions, and stay audit-ready.
Pricing Models

Starter
Perfect for small teams looking for simple and cost-effective solutions
🟢 Core GRC modules
🟢 Real-time reporting
🟢 5 heavy & 50 light users
🟢 Add-on options for a tailored experience

Professional
Ideal for mid-sized businesses that need flexibility and scalability.
🟢 Core GRC modules
🟢 Real-time reporting
🟢 API integration with existing system
🟢 Customer support for smooth operations
🟢 15 heavy & 150 light users
🟢 Add-on options for a tailored experience

Enterprise
Built for large enterprises with complex workflows and high user demands.
🟢 Core GRC modules
🟢 Audit module
🟢 Real-time reporting
🟢 API integration with existing system
🟢 Dedicated customer success
🟢 50 heavy & 500 light users
Real Results, Real Impact
Faster risk response
Efficiency gains
More efficient compliance execution
Cost reduction
Enterprise-grade security
Data Protection
ISO/IEC 27001 certified to ensure your organization meets global standards for information security and governance.
Control Assurance
ISAE 3402 Type II verified, with independently audited internal controls that guarantee service reliability and compliance.
Financial Sector Readiness
FSQS-NL registered — pre-qualified for procurement by leading banks and insurers in the Netherlands.









.png)



